As technology advances, the use of digital platforms increases over time. These digital platforms can simply record all the information that we added or provided, the things we browsed, or even the people we contacted. Do you know that there’s a feature called digital footprint? Are you aware of how to protect your digital footprint? You might juggle a lot of questions inside your head. To make it simple yet precise,
Digital Footprint is about the slightest activity you do online. It could be browsing, shopping, networking, marketing, dealing, etc. the actions you do on the internet, or your social media leave a digital shadow.
So how do you protect your digital footprint?
If you think that you are protecting the movement and things have been erased, then you are in fool’s paradise. The internet surrounds the world we live in – it is merely unimaginable without it.
According to Statista, there are 4.57 billion internet users globally that roughly encompasses almost 60% of the total population. Out of which 4.17 billion users are immobile internet users. So, do you get it? Leaving the digital footprints is like leaving the door wide open – anyone, anytime, could come in and explore without our consent. Ultimately, it might make sense to take advantage of dark web monitoring.
And when we move to social media users, the score is eye-opening. There are 3.96 billion social media users in the world. Even businesses of all kinds, whether big enterprises or small using social media marketing to take the plunge and more leads.
What Image Can Be Seen Through Your Digital Footprint?
The digital world is like a patch of mud – when you walk through it, you leave the footprints, and if your footprints are not adequately handled or removed, you are about to drown, depending upon the left marks.
Seeing your digital footprints leave a perfect image. It is like leaving the dots that can easily be connected. It is time to remove all the negativity and show the positive attributes of your character.
It’s indeed a good idea to leave positive digital footprints. Why? Because people who need to assess you without telling you can easily do that. For example, in schools and colleges for the students, employers can evaluate the candidate’s character and law enforcement for activity tracking.
Categories of Digital Footprint
The digital footprint can be categorized into two major categories. One is active, and the other is passive. Both of these digital footprints are based on the kind of evaluation you required.
Active Digital Footprint
When you made deliberate choices on the internet, that time, you left an active digital footprint. Whatever you are posting on your digital platforms or being more precise on the social media platforms is considered an active digital footprint.
Same goes with the login type when you go on to a similar site, the entries you make while logging in are the active digital footprint.
It could be understood with these examples;
- Whenever you share something on your social media platforms such as Facebook, Twitter, or Instagram, it gets prone to digital footprints.
- Whenever you fill in the online form, you provide in the details of your contacts and accommodation. These are another example of active digital footprints.
- Another example that takes place on the list is when you agree to the cookies on your device by the browser.
Passive Digital Footprint
Passive digital footprints on the other end are those which you leave behind unintentionally. You don’t know what you are leaving behind, but you do!
It happens when the websites that require information and continuously visit them are piling the passive digital footprint. You never intentionally do that, it all occurs unintentionally as you never agreed to give the data. As soon as your device’s IP address is connected with its website, this process begins.
These three examples would help you out in understanding the picture.
- There are tens of thousands of websites that ask you to install cookies and sometimes without even asking. It is when you shared the details with them, and you don’t even know about it.
- Many times when you share, comment, or even like the post on your social media, that time, you also become the victim of passive digital footprint without even knowing it.
- It happens most of the time when you use some of the apps and websites that use your live location to track you and pinpoints you.
14 Tips to Protect Your Digital Footprint
Have you ever considered the available options for reducing your digital footprint or the ways to protect your digital footprint? If not, then you should.
Here are the top fourteen steps or digital footprint tips that would drive you to consider what to do before leaving a digital footprint.
Privacy Settings Must be Triple-checked
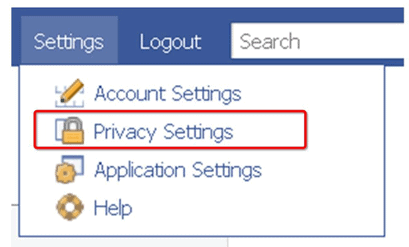
A privacy setting is a step that is paramount on social networking sites. You use social media platforms to connect with the people. Privacy settings are in your hand – it is merely the way you want them to be.
The most understood use of social media platforms is to connect with the people – friends, relatives, or even to the unknowns to grow the acquaintances. The simple use could be a leaking factor of your valuable information.
The information you provided has to be set in such a way that it will not get publicized. People recommend doing giving it double-check, whereas I prefer to give a triple-check to all the settings that you have initiated.
Make it crystal clear that all the information that you have provided must be visible to the known and connected ones. It shouldn’t go in the hands of unknown people.
Create Sturdy And Solid Passcodes
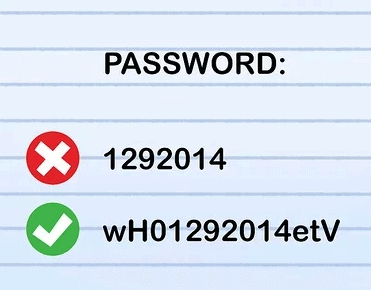
Make sure the passwords you create for your social media handlings must be sturdy, stable, and memorable. Not just the first time – but whenever even you change or shift on to the new platform.
Again, creating or setting a passcode is in your hands. According to estimation, more than half a million passcodes get stolen every day, and more than 1 billion accounts of different platforms are hacked.
Your passcode has to be healthy and the one that you can easily recall. If you are creating the one like ‘123456’ or ‘john12345’, etc. then the chances of getting your account and passcode hacked are higher.
As 51% of the total users create passcodes that are used for the work and personal platforms. So if it is too easy to crack, then your personal but your work information or data are also on the verge to leak.
Make it strong with at least 8-12 characters with capital and small characters and, most importantly, easy to recall and memorize. According to statistical calculation, around 53% of the people rely on their memory to manage the passcodes.
Upgradation Of The Software Must Be Done
Software upgradation is another thing that can be effectively used for erasing the left digital footprint. There is much software that is continuously updating and tracking the digital footprints you leave.
Now, the question that comes here is how this situation could be met? In order to cope with it, you must have antiviruses to run on different software.
Running spontaneous updates and antiviruses will help you stay in the loop and update. If you don’t practice or implement this, your software is vulnerable to attack by hackers.
Double-Check Your Mobile Use
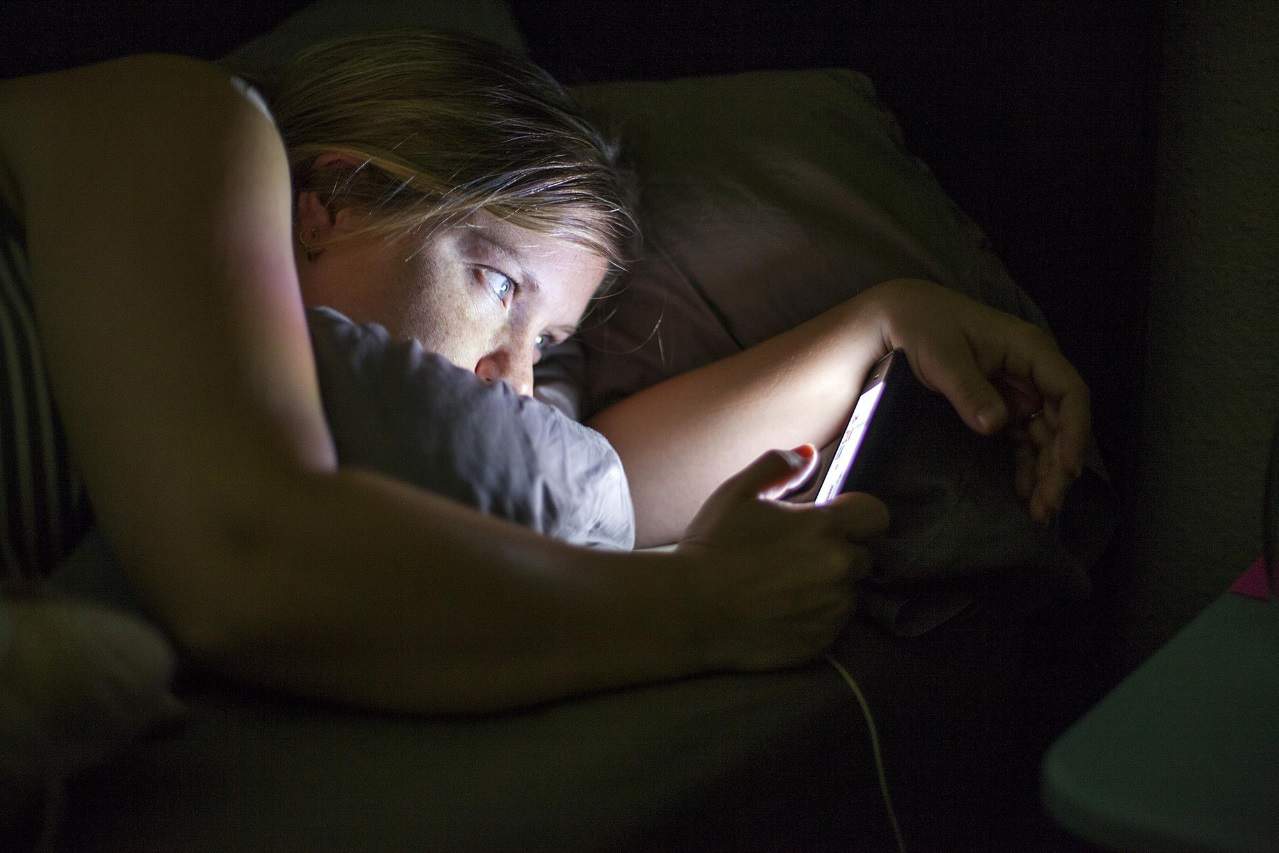
Another thing that happens very frequently is that most of the people lost or misplace their cell phones. The only way that your data or information isn’t compromised is by having the security checks on the cell phone. Earning a certification like CompTIA Security+ validates your ability to implement these security measures and protect sensitive information. To further bolster your preparation, consider utilizing CompTIA Security+ Practice Test Dumps as a valuable resource.
The timely review is also of great significance. If you review the apps that you don’t use on your mobile devices, you can delete them from your cell phones, and if, unfortunately, your cell phone got lost or misplaced, your precious data isn’t leaked, and you secured leaving the digital footprint back.
The applications you install on your phone require an agreement from you before kicking off with them. In that agreement, they mostly shared the details of where the information can be shared, etc.
Now, as most people do, if you just accepted the agreement and without digging in shared your valuable data, your digital footprint is at the higher risk of getting exploded to the public, you might not want to deal with.
Determine And Realize The Search Behavior
It is paramount to determine the behavior of search engines or even social media platforms. Having a digital footprint has another side too sometimes, the authoritative party isn’t you – means that the control isn’t in your hands.
Like this example, Facebook is the most frequently used social media platform of 2020 records and has access to even scrap of information to analyze, understand, and determine the behavior and create demographics based on marketing.
It often happens when you click on the Facebook ads, and some of your details have been shared. So limiting the information even at the most used digital platform can decrease leaving digital footprints.
Keep Updated List of Accounts
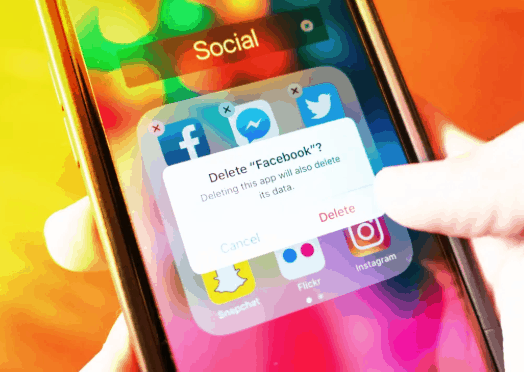
Keeping the updated list of accounts is like the game in control. A double or triple check must be done to eliminate or erase all those apps that you don’t use. It is better to have empty spaces on your cell phones or tablets than to have filled them up and risking leaving the digital footprint.
When you have the list of accounts that you commonly use, you can easily erase the rest. Create a schedule of reviewing and analyzing the application after every 3 or 6 months to keep intact.
Never Publicize Your Details
I hope that until now, you have realized why leaving a digital footprint is the biggest mistake. The pro tip here is never to post personal information online on any social media platform. To many of the users, it might not seem something that should be taken care of. But, in the widened horizon, the results are pretty ugly.
Your privacy can be invaded if you provide your key information online. The hackers of today are intelligent and wiser than we think! Breaking the barrier or entering isn’t tough for them if they get the information like a ready to eat platter.
If the application you are entering on is a must needed form without which you can’t survive, add the necessary information, and never fill in the optional portion. Privacy is at risk for those who publicize themselves.
Implement The Secrecy Mode
It is rightly said that;
‘No one ever approaches perfection except by secrecy.’
(William Hazlitt)
But what if you’re asked to name three actions that leave a digital footprint? As technologies advances, breaching becomes easier. However, you have the option to improve your browser’s settings. If you use this method, you can easily browse the websites without leaving a single mark behind. The actions will become private, and you gain control.
This process indeed helps in minimizing the risk of leaving digital footprints, but it would not make everything invisible.
Deactivation Of Old Email Accounts
Deactivation of old email accounts is also another step forward to erasing digital footprints. The email address you created in the early days of digitalism needs to be redefined or deactivated.
Being in infant to digitalism, you might have added all the necessary information without even giving it a thought. Now, after getting to know the possible threats from digital footprints, you are on to deactivation.
The abandoned accounts will provide an open gate to the invaders. It is better to eliminate all the email accounts, instead of leaving them and creating possible menaces.
Prioritize The Use Of VPN
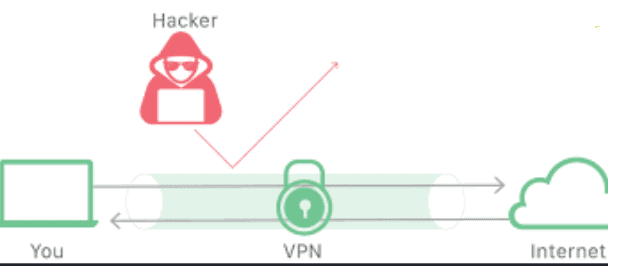
Virtual Private Network (VPN) is a software or tool that gives privacy or anonymity by setting a privacy network from the public connection. This security firewall gives you an extra layer that protects your security from all breaches.
By using a virtual private network protection, you reduce the risks of tracking down by the websites. So how does the VPN server work?
It works by masking your IP address, which increases the protection level, and your online actions are almost untraceable. There are plenty of VPN providers in the market. Get the best that matches your requirements and affordability.
Search Yourself On Search Engines
Try to go on different search engines and type your name by adding first and last names accordingly. If you get in the top searches on the Search Engines Result Pages (SERPs), then view where your name has been popping up, ask the website running administrator to take down your name.
You can also activate Google Alerts that can help you in being vigilant to track your name. By setting up Google Alerts, when your name pops up or matches somewhere, the notification will give you the alert.
You might not have wondered, but several white pages providers and real estate’s have much of your information than you ever disclosed. Your email address, contact numbers, and sometimes residential addresses are also quite easy to hold. You can simply go to the website and ask the site to remove your details. Removing your online digital data is a proactive step to protect your privacy and reduce the risk of identity theft or other harmful consequences.
Use Digital Tools To Manage Your Digital Footprints
There are a host of application add-ons and browser extensions with which you can limit the vulnerable personal and work information. Also, some other plugins and extensions can erase the website tracking, and thus your valuable information is protected.
Digital tools are advancing most successfully. These tools can help you reduce your digital footprints significantly.
Distance Yourself From Database Mailing Lists
Sometimes while you are shopping online or ordering food or even watching online streaming, you agree to several mailing lists. These mailing lists require a few points of information, and with that, they can have access to a broader picture.
If you had done that unknowingly in the past, now is the time to think it over and unsubscribing yourself from all the platforms that required even the slightest of information and are irrelevant to you.
Don’t Enlist Yourself For Silly Surveys
The internet is filled with preposterous and absurd surveys. Online games, forms, and even people are asking for random daft surveys to which we unknowingly show our willingness and fill the form to support the cause or to get accessibility to play the game or join the community.
This act is another addition to the wrongful acts. Leaving digital footprints will be increased with these nonsense surveys that are of no benefit to us.
Conclusion
The use of the internet and social media handlings should be done with extreme caution. If you not cautious or conscious, then you are on the brink of embedded threats in digital footprints.
The threats we face while being online are numerous, ranging from online data theft to invasion of privacy, cyberbullying, and fraud. When you learn the importance of what is increased footprint on social media, the right practices at the right time will definitely help you from being vulnerable and better protect your digital footprint.
Numerous methods can be taken to overcome the digital footprint.
[starbox]

